Identity Is the New Perimeter: Credential Compromise in the Modern Enterprise
How attackers have shifted from breaking through walls to simply walking through the front door, and what you can do about it.
Introduction: The perimeter is dead. Long live identity.
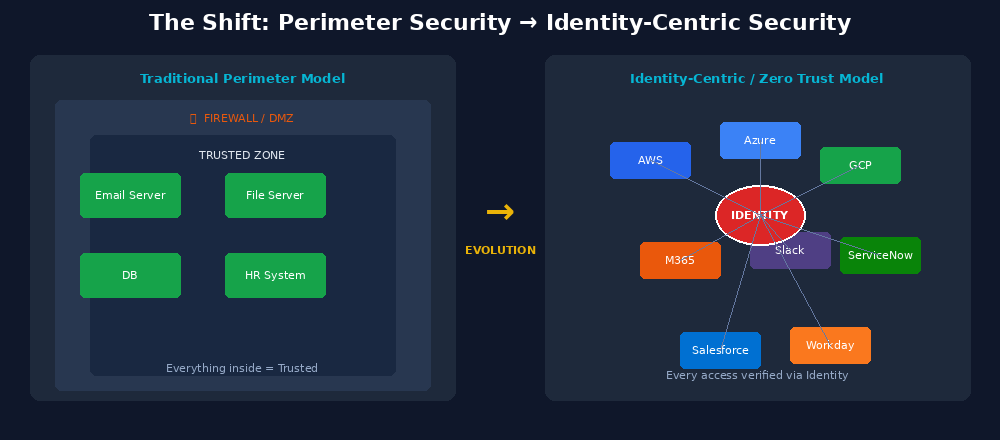
For decades, enterprise cybersecurity was built on a foundational assumption: draw a line around your network, fortify it, and anything inside that line is trusted. Firewalls, intrusion detection systems, and DMZs were the vocabulary of defense. If you could keep the bad guys out, you were safe.
That model is gone.
The modern enterprise does not live behind a single perimeter anymore. It lives in AWS, Azure, and GCP. It operates through Salesforce, Workday, Microsoft 365, Slack, ServiceNow, and hundreds of other SaaS applications. Its employees work from home, from coffee shops, from airport lounges, authenticating from IP addresses that shift daily. Its contractors access systems through their own unmanaged devices. Its developers push code through CI/CD pipelines that themselves hold privileged credentials.
In this world, the only thing that consistently defines who should have access to what is identity. Identity has become the primary battleground of modern cybercrime.
The numbers are sobering. According to the Verizon Data Breach Investigations Report, credentials are involved in the overwhelming majority of web application breaches. CrowdStrike has reported that attackers are increasingly able to move from initial access to lateral movement in under seven minutes once they have valid credentials. IBM's Cost of a Data Breach Report consistently places the average cost of a breach well above four million dollars, and breaches involving stolen credentials take longer to identify and contain, driving costs even higher.
This is not a niche problem. It is the defining cybersecurity challenge of our era.
The attack surface: why identity is so exposed
Before diving into specific attack techniques, it is worth understanding why identity has become such a rich target.
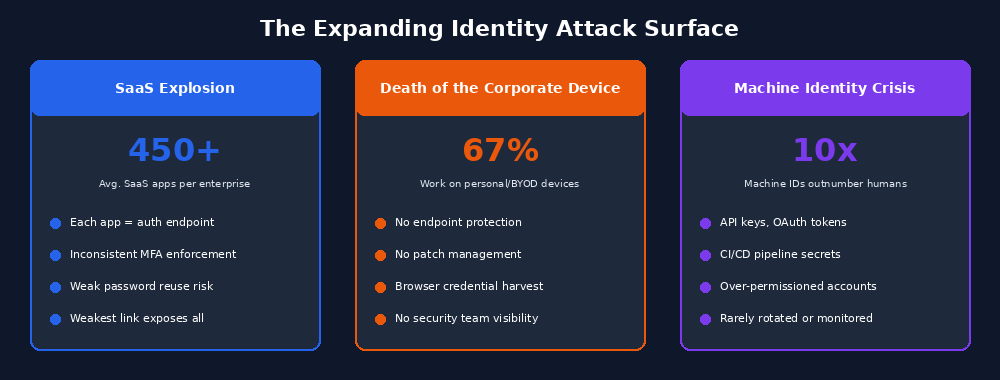
The SaaS explosion
The average enterprise now uses hundreds of SaaS applications. Each one is an authentication endpoint. Each one potentially holds sensitive data. Each one has its own identity model, its own access controls, and its own security posture, which may or may not align with your organization's standards.
When a user has accounts in 150 different SaaS applications, the probability that at least one of those accounts is misconfigured, uses a weak password, or lacks MFA approaches certainty. Attackers do not need to breach your crown jewels directly. They just need to find the weakest link in your identity chain.
The death of the corporate device
In a pre-cloud world, corporate devices sat on corporate networks. Today, a significant portion of work happens on personal devices, managed with varying degrees of rigor. BYOD policies mean corporate credentials are stored in browsers on machines that may have no endpoint protection, no patch management, and no visibility for your security team.
When malware infects a personal laptop and harvests the browser's saved credential store, it may exfiltrate credentials for dozens of corporate and personal applications simultaneously.
The machine identity crisis
Human identities are only part of the problem. Modern infrastructure is riddled with non-human identities: service accounts, API keys, OAuth tokens, certificates, CI/CD pipeline secrets, and cloud IAM roles. These machine identities often outnumber human ones by a factor of ten or more, and they are routinely over-permissioned, poorly rotated, and rarely monitored with the same rigor as human accounts.
A leaked API key hardcoded into a public GitHub repository. A service account with domain admin privileges that has not been reviewed in three years. A long-lived OAuth token that grants an abandoned third-party integration access to an entire Microsoft 365 tenant. These are exactly the identity vulnerabilities attackers actively hunt for.
The attack playbook: how credentials get compromised
Attackers have developed a sophisticated, multi-layered arsenal for stealing and abusing credentials. Understanding these techniques is a prerequisite for defending against them.
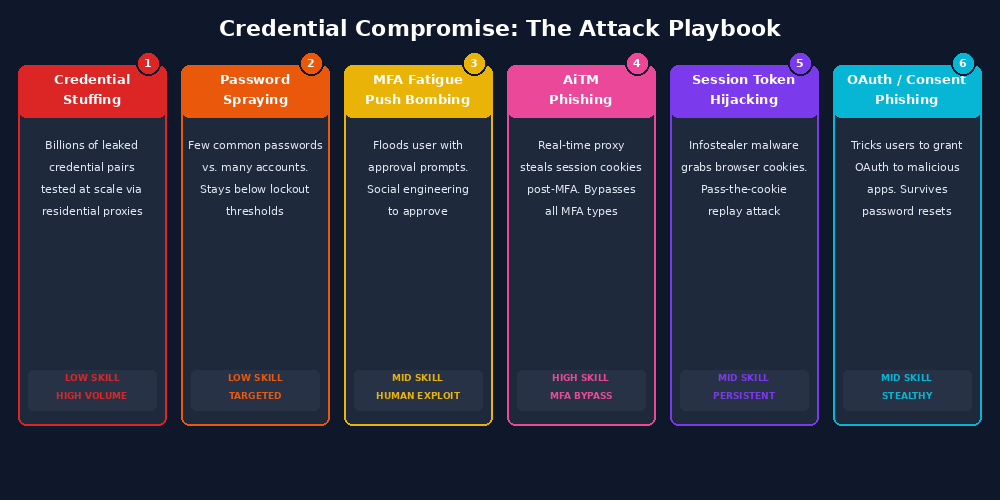
Credential stuffing
Billions of username and password combinations from historical data breaches are freely available on dark web forums and Telegram channels. Credential stuffing is the automated testing of these stolen pairs against target login portals. Because users reuse passwords across multiple services, a credential leaked from an unrelated breach may still grant access to your VPN, HR platform, or cloud console years later.
Modern credential stuffing is highly distributed. Attackers use residential proxies, CAPTCHA-solving services, variable timing, and rotating user agents to mimic legitimate traffic and evade simple detection.
Password spraying
Password spraying takes the opposite approach: instead of trying many passwords against one account, attackers try a small number of common passwords across a very large number of accounts. The objective is to stay below lockout thresholds while still capturing the weak, predictable passwords users choose in real environments.
This technique is especially effective against Microsoft 365, Active Directory, and VPN portals, and it is frequently used to gain an initial foothold in targeted attacks.
MFA fatigue
Push-based MFA improved security for a time, but attackers adapted. MFA fatigue, also known as push bombing, abuses the user experience of repeated push notifications. When an attacker already has a valid username and password, they can trigger repeated prompts until a frustrated or confused user finally taps Approve.
This was a central tactic in the 2022 Uber breach, where the attacker combined repeated MFA prompts with social engineering to get the user to authorize access.
Adversary-in-the-middle phishing
AiTM phishing is more dangerous than traditional fake login pages because it proxies the real authentication experience in real time. The victim believes they are interacting directly with Microsoft's login page. In practice, they are passing through the attacker's relay.
Once the victim completes MFA, the attacker captures the authenticated session cookie. At that point, the attacker can often access the account without needing the password or the MFA device again.
Session token hijacking
Browser-based infostealer malware such as Redline, Raccoon, and Vidar harvest session cookies directly from local browser storage. With a valid session token, an attacker can replay that session and bypass authentication entirely, including MFA.
Underground markets have sold not just passwords, but complete browser fingerprints that make it easier to impersonate victims convincingly enough to evade fraud controls.
OAuth abuse and consent phishing
Cloud ecosystems depend heavily on OAuth 2.0 and delegated authorization. Consent phishing tricks users into approving malicious applications that request legitimate-looking permissions. Once the victim grants access, the attacker may hold a long-lived token with broad access to Microsoft 365 or other platforms.
This is particularly dangerous because changing the password may not remove the malicious authorization grant. The compromise lives in the token, not the password.
The kill chain: what happens after initial compromise
Understanding how attackers get credentials is only half the story. What they do with those identities reveals the full scope of the threat.
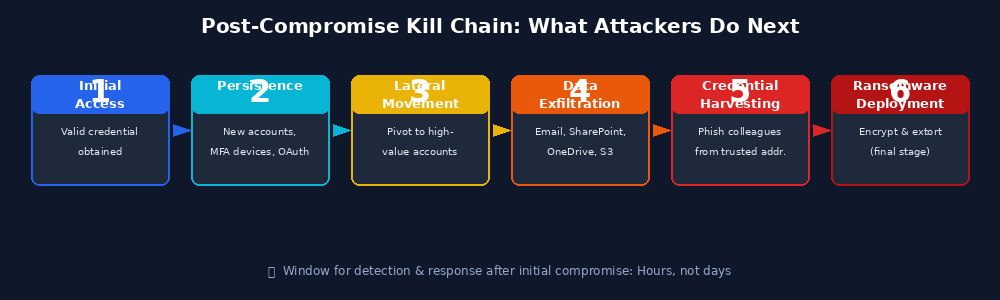
Once attackers gain a valid identity, their goals typically include persistence, lateral movement, data exfiltration, harvesting additional credentials, and eventually ransomware deployment. A single compromised identity with the right privileges can unlock an enormous range of systems in Microsoft 365, Azure AD, and connected business applications.
The speed of modern attacks makes early detection critical. The detection window after initial credential compromise can be measured in hours, not days.
The defense framework: building identity-centric security
The good news is that while the threat landscape is serious, the defensive foundations are well understood. The challenge is disciplined implementation.
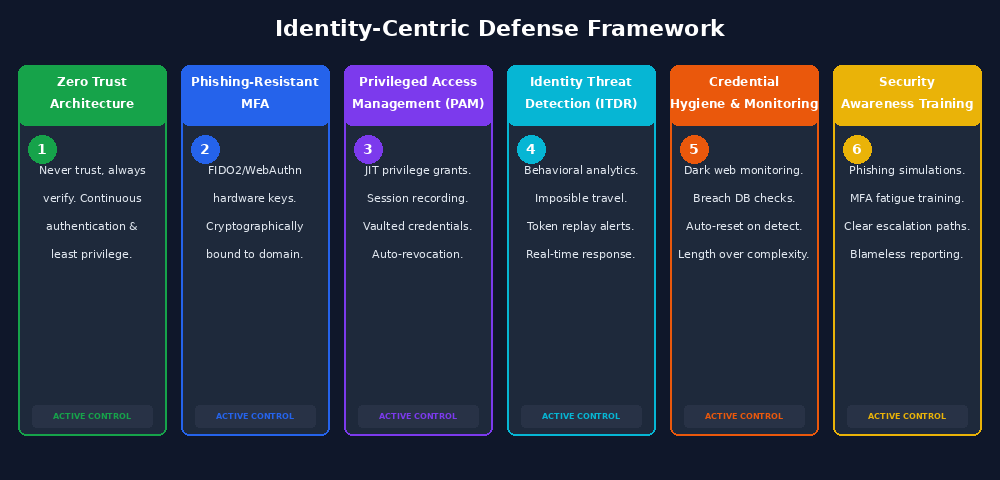
Zero Trust architecture
Zero Trust is not a product. It is a philosophy: never trust, always verify. No user, device, or network location is inherently trusted. Every request must be authenticated, authorized, and continuously evaluated.
In practice, that means verifying identity on every access request, enforcing least privilege, evaluating device and behavior signals continuously, and assuming breach when designing access patterns.
Phishing-resistant MFA
Not all MFA is equal. Push MFA is vulnerable to fatigue attacks. SMS-based codes are vulnerable to SIM swapping. Time-based authenticator apps are still vulnerable to AiTM phishing.
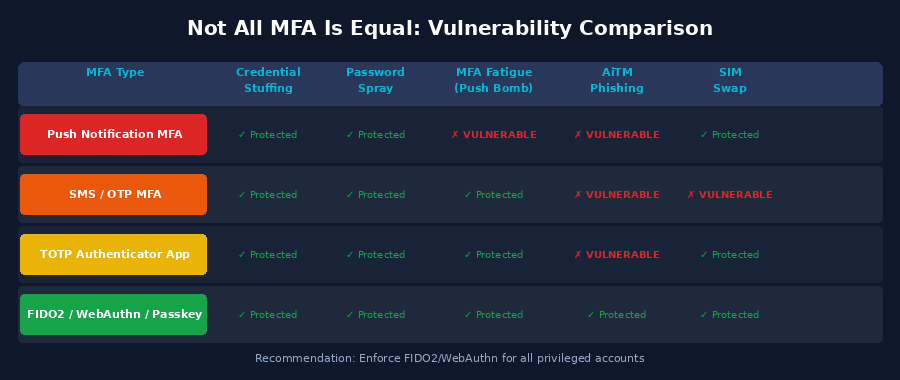
Phishing-resistant MFA using FIDO2, WebAuthn, security keys, or passkeys is cryptographically bound to the legitimate domain. That makes it significantly more resilient to modern phishing relays and token capture attacks.
Privileged access management
Privileged accounts are the highest-value targets in the environment. PAM solutions help by enforcing just-in-time access, requiring stronger workflows for sensitive operations, recording privileged sessions, and vaulting credentials so they are not broadly known or reused.
Continuous identity threat detection and response
Modern identity threat detection and response platforms analyze authentication events, access patterns, and behavioral signals in real time. Signals such as impossible travel, anomalous MFA prompts, token replay, mass email forwarding, large data downloads, and new OAuth grant creation can reveal attacks that traditional logging reviews miss.
Credential hygiene and exposure monitoring
Organizations should monitor continuously for exposed credentials across breach datasets, dark web sources, and paste sites. When exposures appear, password resets and session invalidation should happen immediately.
Password policies should prioritize length, reject known compromised passwords, and avoid predictable forced rotation patterns that push users toward weak choices.
Security awareness training
Technical controls need human reinforcement. Employees should know how to recognize phishing attempts, suspicious MFA pushes, and abnormal login prompts, and they should have a clear, low-friction way to report them. Early reporting can be the difference between a contained event and a major incident.
The regulatory and compliance dimension
Identity security is increasingly a regulatory requirement, not just a best practice. NIST 800-63 provides digital identity guidance. PCI DSS 4.0 strengthens MFA requirements. SOC 2 auditors scrutinize access controls and offboarding. HIPAA enforcement actions have cited weak authentication controls as contributing factors in breach penalties.
For regulated organizations, the business case is both risk reduction and compliance readiness.
The road ahead: AI and the escalating identity war
The identity threat landscape is not static. AI is accelerating both offensive and defensive capabilities.
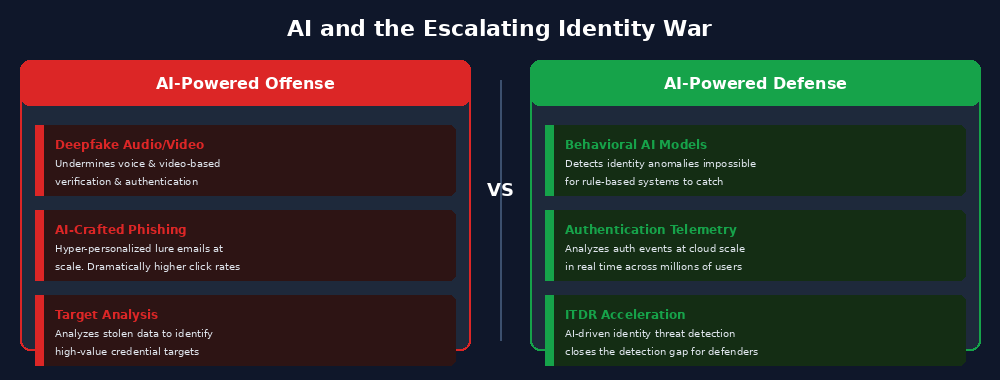
The offensive dimension
AI-generated deepfake audio and video are making voice and video-based verification less reliable. AI-assisted phishing tools can craft more personalized lure content at scale. AI is also being used to analyze stolen data for high-value identity targets with greater precision.
The defensive dimension
Behavioral models can spot identity anomalies that rule-based systems would miss. AI is helping security teams analyze authentication telemetry at the scale modern cloud environments generate. Organizations investing in mature identity analytics are beginning to close the detection gap.
Conclusion: identity is your security posture
There is no longer a meaningful distinction between identity security and security. In the modern enterprise, identity infrastructure is security posture. The organizations that understand this and invest accordingly will be positioned to defend against the dominant threat vector of our time.
The perimeter is gone. Identity is what remains. Protect it like the business depends on it, because it does.